INE Year 2 Summer Workshop (2003)
Building a Hotel Broadband Service System (HBSS)
Version 1.2
I.
Background
Information
In this workshop, you will build a Hotel Broadband Service System (HBSS) which will provide the following functions for the broadband connection in hotel rooms:
1. Access Control
2. Network Authentication
3. Accounting for Network Connection Billing
Access Control
User in a hotel room can connect to the hotel intranet through DHCP. Before authentication, the user cannot connect to any host. Any web page access (i.e. 80 port access) will be redirect to a network authentication web page.
Network Authentication
User registers his/her broadband connection by login to the network authentication web page. The HBSS will authenticate the user according to the user name, user credit card number, and the user room number (i.e. the connected switch port. You can get this information from your core switch through snmp or telnet script). If the authentication successes, the HBSS will open all network connections for the user and stop the web redirect. If the authentication fails in three consecutive times, the HBSS will send an alert to the security unit and technical unit to follow up the incident accordingly.
Accounting
The HBSS begins to time the network connection once the user has successfully login the network authentication web page and stop the timing when the user disconnects the network (i.e. the switch port link is down). User needs to do the network authentication again when the user reconnects the network. The current billing information will be shown on the customer’s room service web pages for user to query.
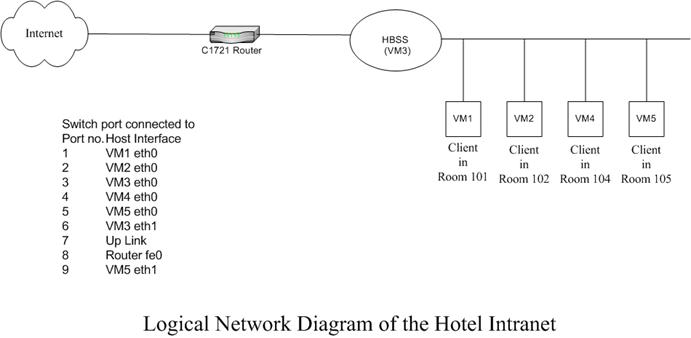
II.
Logical
Network Diagram
III.
IP
Address and Default Gateway
|
Hotel In |
IP address allocation |
Subnet mask |
Default gateway IP |
|
BJ of NSP A |
172.16.98.0/29 |
255.255.255.0 |
172.16.98.254 |
|
CD of NSP A |
172.16.98.8/29 |
255.255.255.0 |
172.16.98.254 |
|
HK of NSP A |
172.16.98.16/29 |
255.255.255.0 |
172.16.98.254 |
|
SH of NSP A |
172.16.98.24/29 |
255.255.255.0 |
172.16.98.254 |
|
BJ of NSP B |
172.16.98.32/29 |
255.255.255.0 |
172.16.98.254 |
|
CD of NSP B |
172.16.98.40/29 |
255.255.255.0 |
172.16.98.254 |
|
HK of NSP B |
172.16.98.48/29 |
255.255.255.0 |
172.16.98.254 |
|
SH of NSP B |
172.16.98.56/29 |
255.255.255.0 |
172.16.98.254 |
|
BJ of NSP C |
172.16.98.64/29 |
255.255.255.0 |
172.16.98.254 |
|
CD of NSP C |
172.16.98.72/29 |
255.255.255.0 |
172.16.98.254 |
|
HK of NSP C |
172.16.98.80/29 |
255.255.255.0 |
172.16.98.254 |
|
SH of NSP C |
172.16.98.88/29 |
255.255.255.0 |
172.16.98.254 |
|
BJ of NSP D |
172.16.98.96/29 |
255.255.255.0 |
172.16.98.254 |
|
CD of NSP D |
172.16.98.104/29 |
255.255.255.0 |
172.16.98.254 |
|
HK of NSP D |
172.16.98.112/29 |
255.255.255.0 |
172.16.98.254 |
|
SH of NSP D |
172.16.98.120/29 |
255.255.255.0 |
172.16.98.254 |
IV.
Specifications of HBSS
- Set up the DHCP server so as to assign IP to clients in hotel rooms
- Set up a DNS server. You can set it to “forward only” with forwarders {137.189.87.1}
- Set up the traffic control to cut connection and redirect web access for all unauthenticated clients
- Set up a database for user personal information (user name, credit card number, and room number) and connection time record for billing.
- Set up an authentication server for network authentication
- Set up secure web server for network authentication web pages.
- Write the program to authenticate the user according to the user name, user credit card number, and room number (i.e. the connected port)
- Write the program to open connection and stop redirect web access for success authentication, and send alert for fail authentication.
- Write the program to record the connection time of the users and post the current billing on the customer’s room service web pages. You may use snmp trap to monitor the switch port link up and down time.
V.
Other
Tasks Specification
- Configure the VM guest hosts and install the necessary tools, such as web browser.
- Configure the switch to build the hotel network infrastructure and support the private VLAN (i.e. client in a hotel room cannot communicate with other clients in other hotel rooms even they are all in the same VLAN. Each client can only communicate with the HBSS)
- Configure the router so as to support Internet routing, NAT, and some basic firewall functions
- Set up the HBSS
VI.
Testing the HBSS
- At your clients, start a web browser (e.g. lynx or netscape) to test the access control before and after the network authentication
- At your core switch, shut down the corresponding port to emulate the network unplug and plug scenarios so as to test the accounting function of the HBSS
VII. Sample data of the customers
|
User Name |
Card No. |
Room No. |
Connection time |
Bill ($1.2/min) |
|
Customer A |
1234567890121394 |
101 |
|
|
|
Customer B |
1234567890129394 |
102 |
|
|
|
Customer C |
1234567890125354 |
104 |
|
|
|
Customer D |
1234567890127086 |
105 |
|
|
VIII. Bonus
- Use LDAP or RADIUS to do your HBSS network authentication and accounting
- Besides supporting DHCP, also support the static IP (plug-and-play solution) for the clients
- Besides counting connection time, also calculate the clients’ Internet traffic (e.g. by netflow) for billing
IX.
References
DHCP Server Package (Only VM3 require to install)
ftp://ftp.cs.cuhk.edu.hk/pub2/redhat/redhat-7.3/en/os/i386/RedHat/RPMS/dhcp-2.0pl5-8.i386.rpm
DHCP mini-HOWTO
http://www.redhat.com/mirrors/LDP/HOWTO/mini/DHCP/index.html
Redhat 7.3 update package
http://updates.redhat.com/7.3/en/os/i386/
MYSQL
Configuring Passwords and Privileges
http://www.cisco.com/univercd/cc/td/doc/product/software/ios120/12cgcr/secur_c/scprt5/scpass.htm
Port Address Translation (IP Masq on Cisco router)
http://www.cisco.com/warp/public/794/827spat.html
Perl Net::Telnet
http://search.cpan.org/author/JROGERS/Net-Telnet-3.03/lib/Net/Telnet.pm
http://www.cisco.com/pcgi-bin/Support/browse/psp_view.pl?p=Software:BBSM